Introduction
Software errors can disrupt work, delay projects, and create unnecessary stress—especially when the cause is unclear. One issue that has recently raised questions in developer forums and IT support discussions is the 2579xao6 code bug. Users encountering this error often report sudden application crashes, unstable system performance, or unexpected interruptions during execution.
If you’re seeing this error message, you’re likely searching for answers about what it means, why it appears, and how to fix it safely. This comprehensive 2025 guide explains the root causes, common symptoms, step-by-step troubleshooting methods, and practical prevention strategies to avoid future occurrences.
Rather than offering generic advice, this article provides structured, professional insights grounded in modern software maintenance standards. Whether you are a developer, IT administrator, or everyday user, you will find clear and actionable solutions below.
What Is the 2579xao6 Code Bug?
The 2579xao6 code bug is typically classified as a runtime or execution-level software error. It occurs when an application fails to perform an expected process due to corrupted files, configuration conflicts, or incompatible system dependencies.
In many cases, the error does not originate from a single source. Instead, it reflects a chain reaction, where one misconfigured component affects the overall stability of the program.
Quick Definition (Featured Snippet Ready)
The 2579xao6 code bug is a system or runtime software error triggered by corrupted files, incomplete installations, or configuration conflicts that disrupt application execution.
Unlike simple warning messages, this issue can halt processes entirely, making timely diagnosis essential.
Common Causes Behind the Error
Understanding the root cause is crucial before attempting any fix. In 2025, most software errors arise from fragmented update cycles, third-party integrations, and inconsistent system environments.
Typical causes include corrupted system files, interrupted software installations, outdated drivers, and registry misconfigurations. Sometimes security software blocks essential processes, mistaking legitimate files for suspicious activity.
Below is a summary of common triggers:
| Cause Category | Likely Impact |
| Corrupted executable files | High |
| Incomplete updates | High |
| Driver incompatibility | Medium |
| Registry conflicts | Medium |
When multiple minor issues combine, they can trigger this specific code failure.
Recognising the Symptoms Early
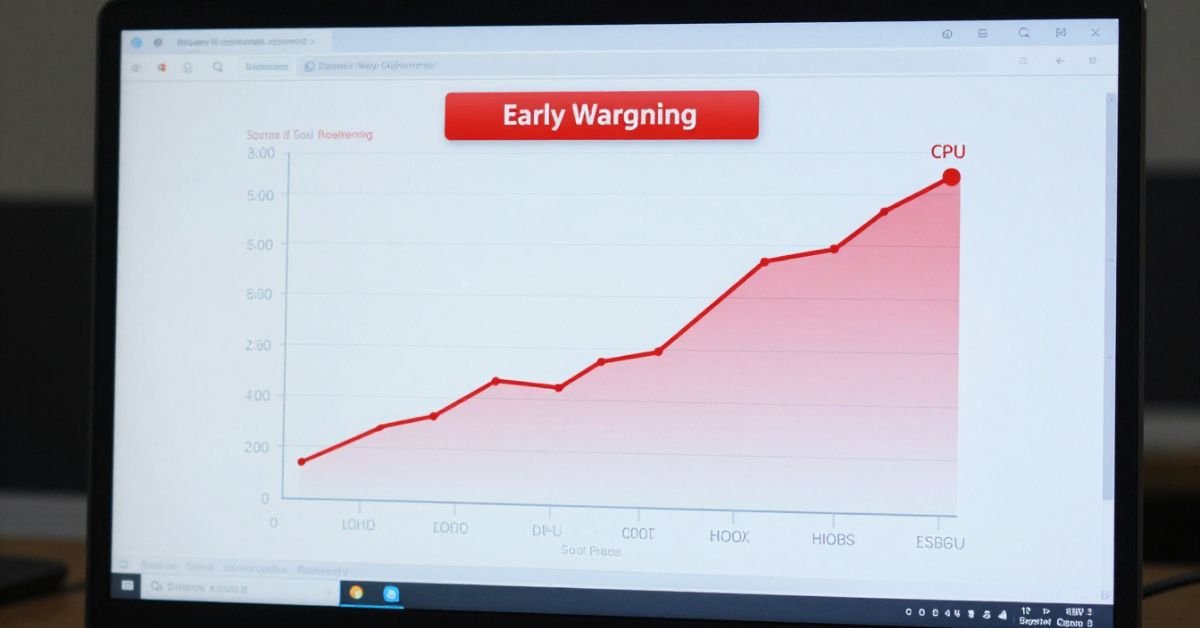
Many users ignore early warning signs, assuming they are temporary glitches. However, recurring issues often signal deeper problems.
Common symptoms include unexpected crashes during startup, system freezing, unusually high CPU usage, and files failing to save correctly. Some users report repeated pop-up errors referencing numeric or alphanumeric codes.
Here is a severity overview:
| Symptom | Urgency Level |
| Random app crashes | Moderate |
| System-wide freezing | High |
| Data corruption warnings | Critical |
If performance degradation becomes noticeable, immediate troubleshooting is recommended.
System-Level Impact and Performance Issues
Software errors rarely remain isolated. When unresolved, they may affect broader system performance. Background retry attempts, memory leaks, and repeated execution failures can increase resource consumption.
Over time, this may lead to slower boot times, delayed file access, or interrupted network communication. In enterprise systems, downtime caused by execution-level errors can disrupt operations and impact productivity.
According to the 2025 IEEE Software Reliability Review, runtime errors account for nearly one-fifth of preventable system downtime incidents. Proactive maintenance significantly reduces this risk.
Step-by-Step Troubleshooting Process
A structured approach improves resolution efficiency. Begin with simple measures before escalating to advanced diagnostics.
First, restart the system. Temporary memory conflicts often resolve after a reboot. Next, check for pending updates for both the operating system and the affected application. Many bugs are resolved through patches released by developers.
Running a system file integrity check is another essential step. On Windows systems, the built-in System File Checker can detect and repair corrupted files. Reinstalling the problematic application may also eliminate incomplete installation artefacts.
If these steps fail, reviewing event logs or error reports can provide deeper insight into execution conflicts.
Advanced Diagnostic Techniques
When basic troubleshooting does not resolve the issue, more advanced methods may be required. Reviewing system logs allows you to identify recurring patterns associated with the error.
Developers may use debugging tools or runtime analysers to trace the fault location within the codebase. IT administrators often inspect registry entries and configuration files to locate inconsistencies.
Here is a comparison between manual and automated repair methods:
| Method | Best For | Complexity |
| Manual file inspection | Technical users | Moderate |
| Automated repair tools | General users | Low |
| Full system restore | Severe corruption | High |
While automated tools simplify diagnostics, experienced users may prefer direct system-level analysis.
Prevention Strategies for Long-Term Stability
Preventing future errors requires disciplined system maintenance. Regular updates ensure compatibility between operating systems and installed software.
Maintaining consistent backups protects against data loss. Monitoring system logs periodically can reveal anomalies before they escalate. Additionally, avoiding unverified downloads reduces the risk of file corruption or malicious interference.
Cybersecurity agencies such as CISA emphasise layered protection strategies, including antivirus updates and secure configuration management, to minimise runtime errors and execution failures.
Proactive maintenance remains more effective than reactive troubleshooting.
Comparing Similar Software Errors
Users often confuse different runtime errors. Understanding distinctions helps avoid misdiagnosis.
| Error Type | Primary Cause |
| DLL Errors | Missing or damaged libraries |
| Registry Errors | Misconfigured system entries |
| Runtime Exceptions | Code execution conflicts |
| 2579xao6 Bug | File corruption or misconfiguration |
Accurate identification ensures the correct repair strategy is applied.
When to Seek Professional Support
If repeated attempts fail and the system remains unstable, professional intervention may be necessary. This is especially important when sensitive data or enterprise applications are involved.
Consider escalation if crashes persist, performance declines significantly, or security vulnerabilities are suspected. Certified IT specialists can perform deep registry repair, advanced debugging, and safe recovery procedures.
Attempting aggressive manual fixes without expertise may worsen the situation.
Future Trends in Software Error Management
In 2025, predictive maintenance tools are transforming system diagnostics. AI-driven monitoring software can detect irregular execution patterns before they trigger major failures.
Cloud-based backup systems now integrate automated patch deployment and anomaly alerts. Zero-trust architectures reduce configuration conflicts by enforcing strict software validation rules.
As technology advances, proactive error detection will become standard practice rather than optional.
FAQs
What causes the 2579xao6 code bug?
It is usually triggered by corrupted files, incomplete updates, or configuration conflicts.
Can it damage my system permanently?
It rarely causes permanent damage if addressed promptly.
Should I reinstall the operating system?
Only if other troubleshooting steps fail and corruption is severe.
Is malware responsible for this error?
Sometimes, but not always; a scan is recommended to rule it out.
How can I prevent it from recurring?
Keep software updated, monitor system health, and maintain backups.
Conclusion
The 2579xao6 code bug represents a complex but manageable software issue. By understanding its causes, recognising early warning signs, and applying structured troubleshooting methods, most users can restore system stability efficiently.
Prevention through regular updates, system monitoring, and disciplined maintenance significantly reduces the risk of recurrence. As software environments continue to evolve in 2025, proactive diagnostics and responsible system management remain the best defence against execution-level errors.